Ever tried to visit a website and got smacked with that dreaded ERR_SSL_VERSION_OR_CIPHER_MISMATCH error? Yeah, it’s one of those SSL headaches that can really ruin your day. Basically, your browser and the website’s server are having a disagreement about how to talk securely to each other - kind of like trying to have a conversation where one person speaks ancient Latin and the other only knows modern English.
This particular error pops up when there’s a mismatch in the SSL/TLS protocols or encryption ciphers between what your browser supports and what the server is offering. It’s frustrating whether you’re just trying to browse the web or you’re a website owner dealing with angry users who can’t access your site.
Don’t worry though - I’ve been wrestling with SSL issues for years, and I’ll walk you through exactly what’s going on and how to fix it, whether you’re on the user side or the server side of things.
Summary
- What’s this
ERR_SSL_VERSION_OR_CIPHER_MISMATCH thing?
Your browser and the website can’t agree on how to create a secure connection - it’s like they’re speaking different security languages.- If you’re just browsing: Usually means your browser is too old, your system clock is wrong, or there’s some network weirdness going on.
- If you own the website: Your server’s SSL setup is probably outdated or misconfigured - time to modernize those security settings!
- Quick fixes to try:
- For regular folks:
- Update that browser (seriously, when’s the last time you did?)
- Check if your computer’s clock is actually correct
- Clear out old cached SSL stuff
- Try a different browser or turn off your VPN temporarily
- Full troubleshooting walkthrough down here
- For website owners:
- Upgrade to TLS 1.2 or 1.3 (anything older is basically ancient history)
- Ditch those weak ciphers like RC4 - they’re about as secure as a screen door
- Make sure your SSL certificate is properly installed and not expired
- Run your site through SSL Labs to see what’s broken
- Complete server-side guide right here
What’s Actually Happening With This SSL Error?
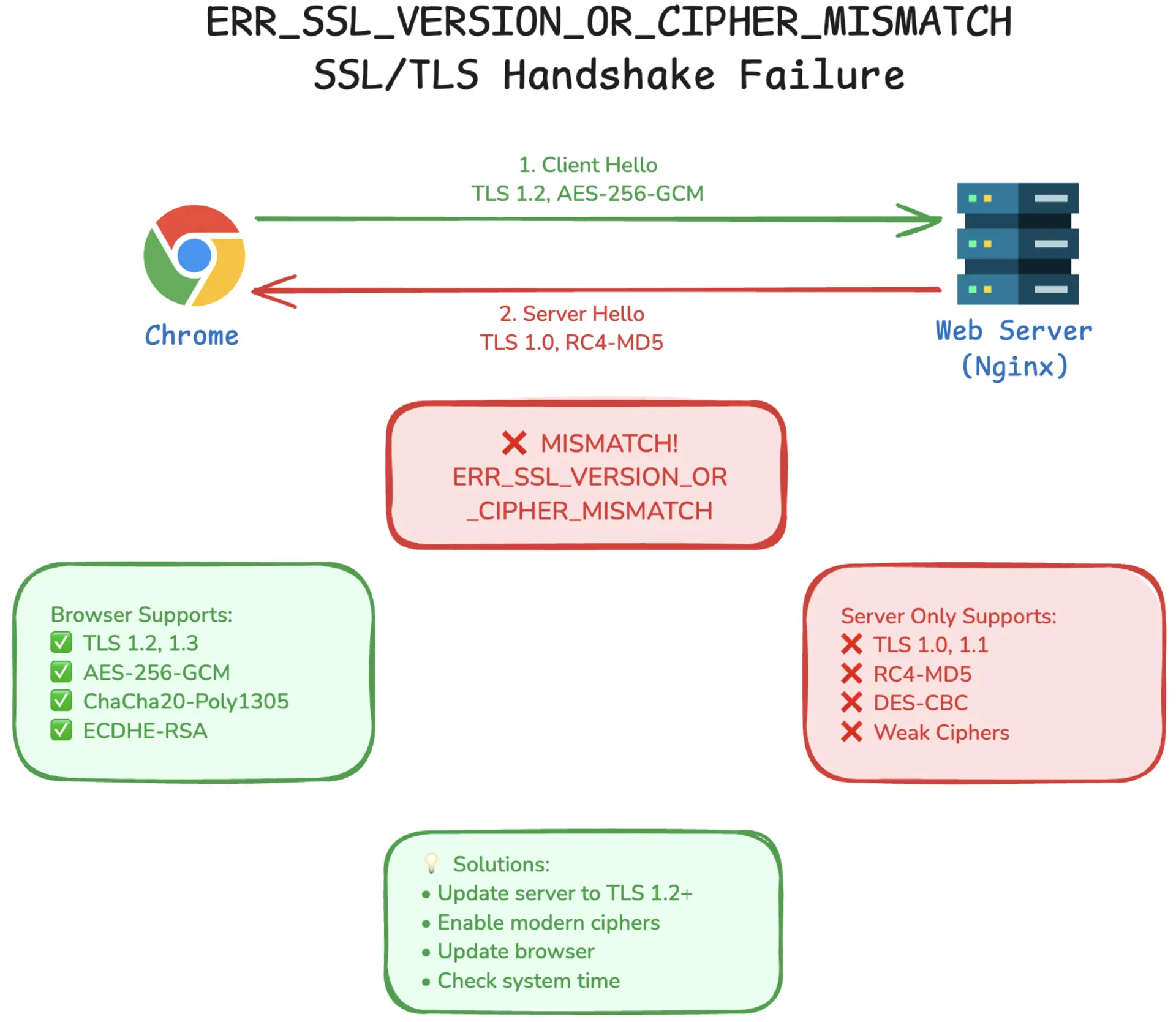
ERR_SSL_VERSION_OR_CIPHER_MISMATCH basically means your browser and the website’s server can’t agree on how to create a secure connection. Think of it like trying to have a secret conversation but you both have different codebooks.
During the SSL/TLS handshake, your browser and the server negotiate which protocol version (TLS 1.2, 1.3, etc.) and cipher suites (like AES-256-GCM or ChaCha20-Poly1305) to use. If they can’t find common ground - maybe your browser only supports modern TLS 1.3 while the server is stuck on ancient TLS 1.0 - the connection fails.
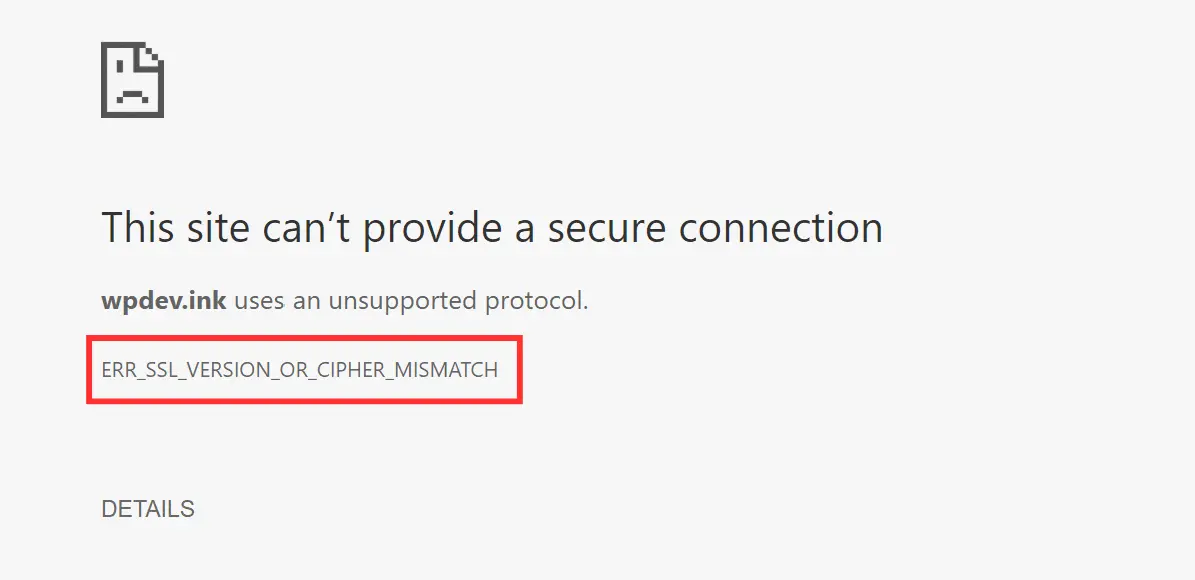
When this happens, your browser throws up its hands and shows you that familiar “connection isn’t private” warning. And honestly, you should listen to it.
If You’re Just Trying to Browse the Web (User Side)
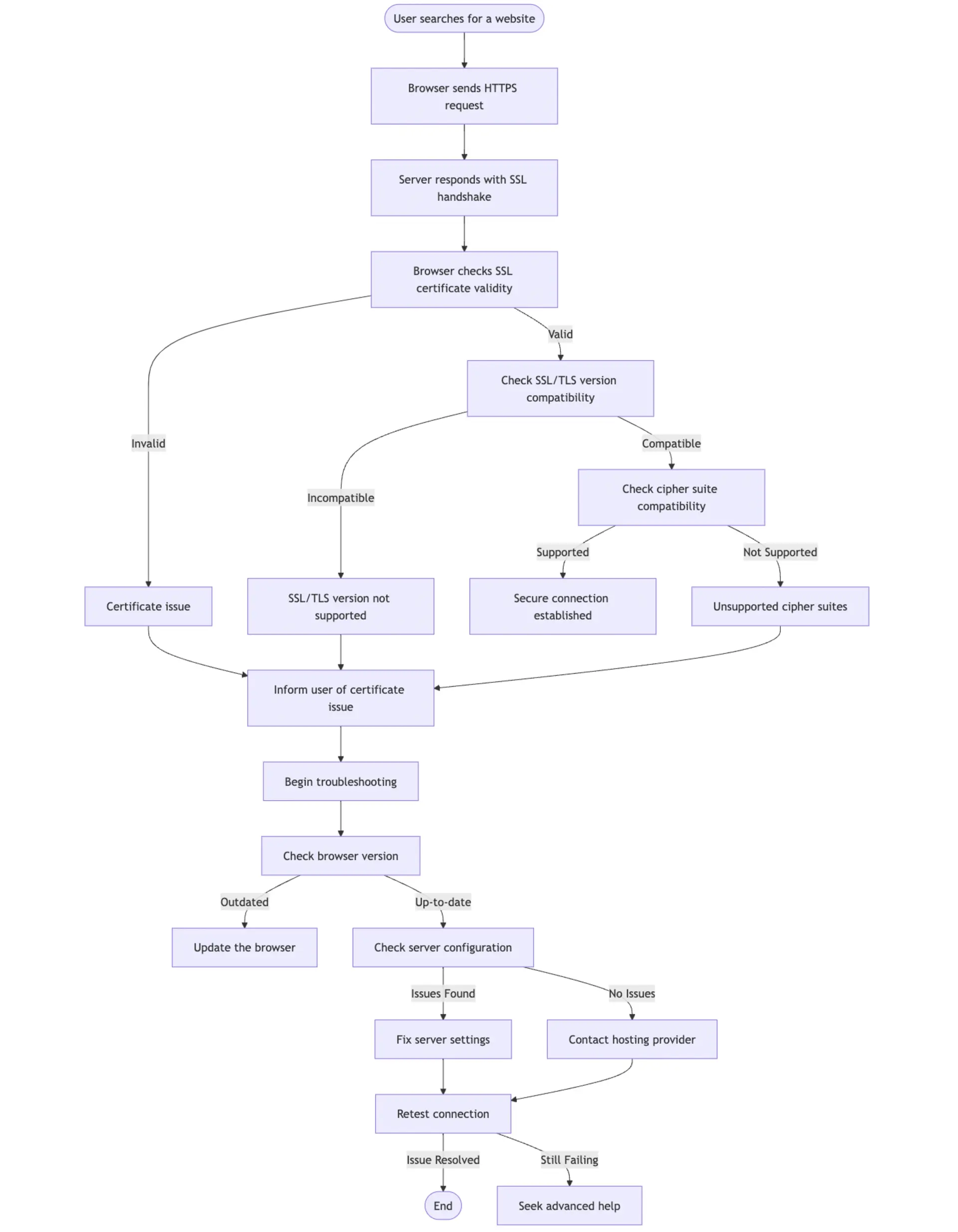
So you’re trying to check out a website and boom - SSL error. Don’t panic! Most of the time, this isn’t your fault, but there are some things on your end that could be causing issues.
What’s Usually Going Wrong
Outdated Browser - If you’re running an old browser, it might not support modern cipher suites like AES-256-GCM-SHA384 or ChaCha20-Poly1305. The SSL/TLS world moves fast, and old browsers get left behind.
Network Issues - Corporate firewalls, VPNs, or proxy servers might block certain TLS versions or mess with SSL connections through their own inspection processes.
Ancient Protocols - TLS 1.0 and 1.1 are dead. Most websites have disabled them due to security vulnerabilities. If your browser tries using these, you’ll get rejected immediately.
Wrong System Time - SSL certificates have expiration dates. If your computer’s clock is wrong, your browser might think valid certificates are expired.
Security Software Interference - Antivirus programs or corporate security tools sometimes intercept SSL connections, breaking the handshake process.
How to Fix This
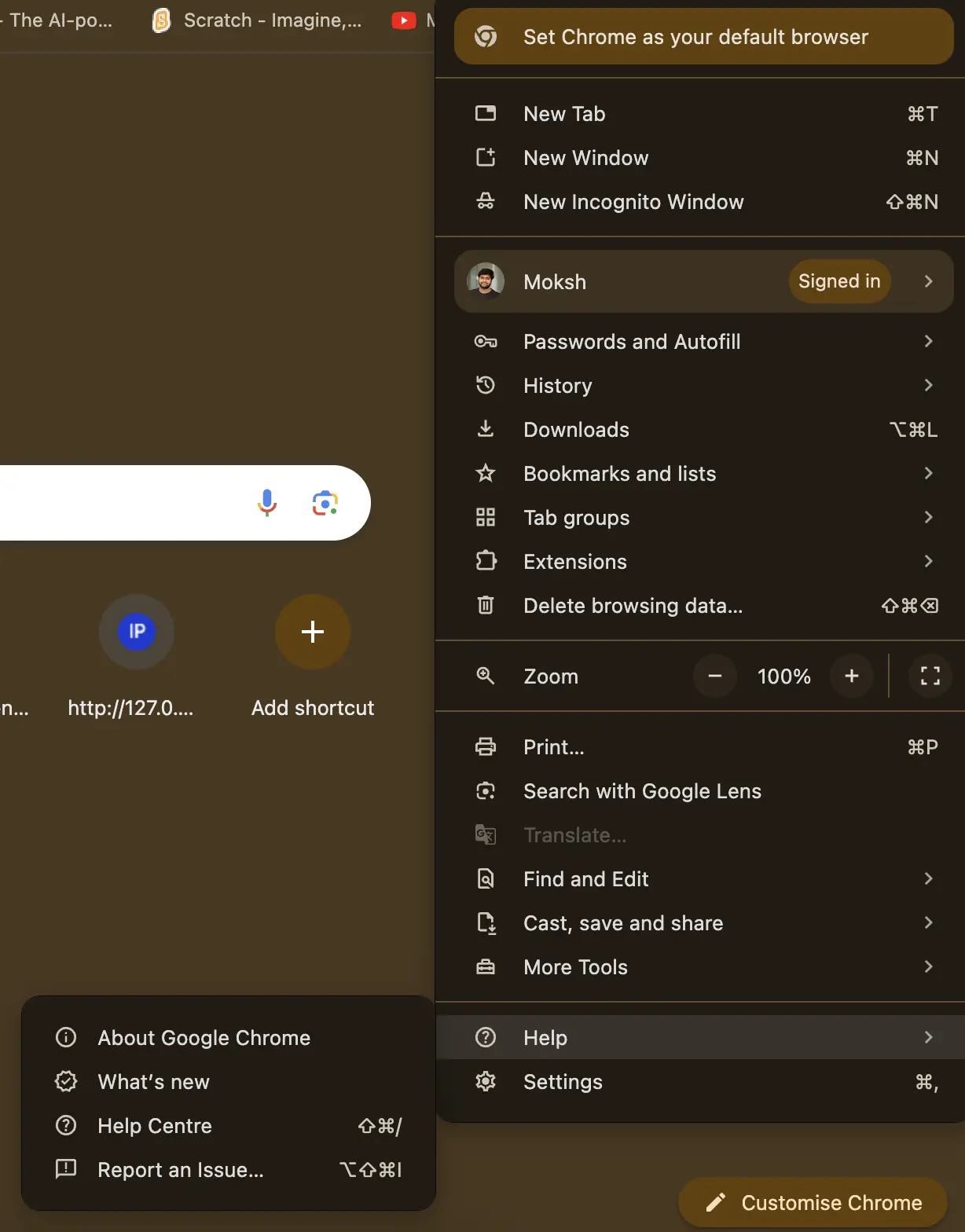
- Update Your Browser
Go to
Help > About Chrome or Menu > Help > About Firefox to check for updates. Modern browsers constantly get new SSL/TLS features and security patches.
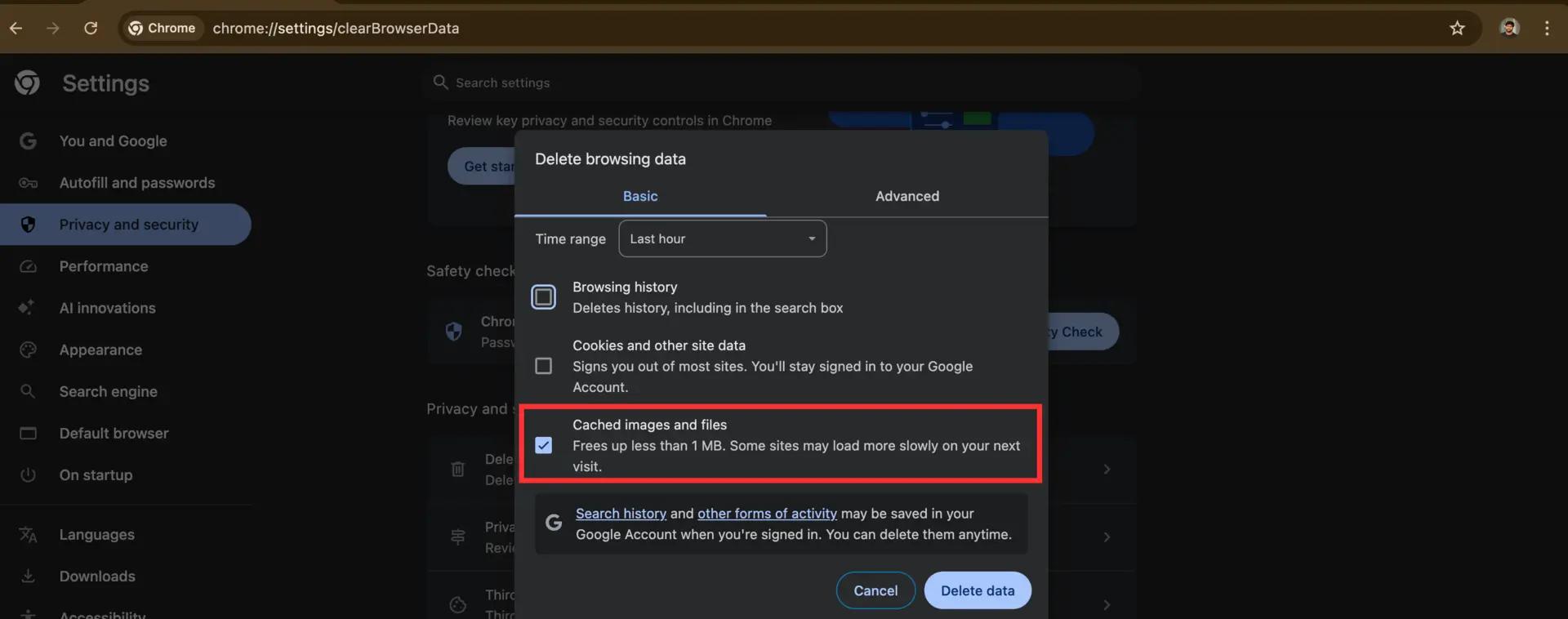
- Clear Browser Cache
Hit
Settings > Privacy and Security > Clear Browsing Data in Chrome. Check “Cookies and other site data” and “Cached images and files.” This forces a fresh SSL handshake.
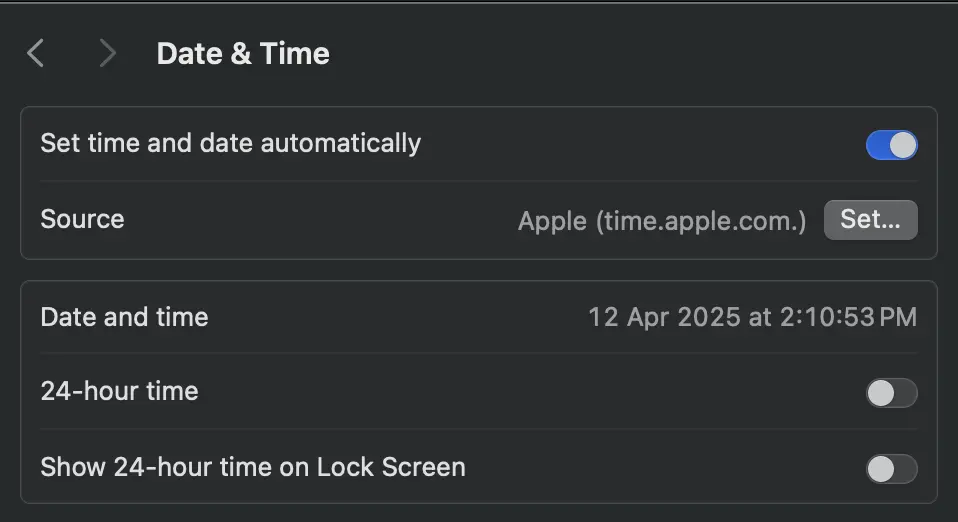
- Fix Your System Clock
SSL certificates have expiration dates. If your clock is wrong, valid certificates look expired.
- Windows:
Settings > Time & Language → “Set time automatically” - Mac:
System Preferences > Date & Time → “Set date and time automatically”
Disable VPN Temporarily
VPNs can route traffic through servers with outdated TLS support or break certificate chains with their own SSL inspection.
Try Different Browser/Device
If Chrome fails, try Firefox. If your laptop has issues, try your phone. This helps identify if it’s your setup or the website.
Don’t Bypass Security Warnings
Resist clicking “Advanced” → “Proceed anyway.” These warnings protect you from real security threats.
If multiple browsers on different devices show the same error, the problem is likely on the website’s end.
If You Own the Website (Server Side)
Getting user reports about SSL errors? Don’t panic, but don’t ignore it either - this stuff seriously hurts traffic and SEO. When users see SSL errors, they bounce immediately, and Google penalizes sites with SSL problems.
Server-side SSL issues are usually your fault (sorry!). Unlike user-side problems, server errors mean your configuration is outdated, misconfigured, or broken.
What’s Wrong With Your Server
Ancient TLS Protocols - TLS 1.0 and 1.1 have vulnerabilities like BEAST, CRIME, and POODLE. Modern browsers have dropped support completely.
Weak Ciphers - RC4, DES, and MD5-based ciphers are broken. RC4 has keystream biases, DES uses tiny 56-bit keys, and MD5 has collision vulnerabilities.
Certificate Issues:
- Self-signed certificates - browsers don’t trust them
- Expired certificates - obvious problem
- Missing intermediate certificates - breaks the trust chain to root CAs
- Domain mismatches - certificate for “example.com” but users access “www.example.com”
Server Misconfigurations:
- Conflicting SSL directives
- Poor SNI (Server Name Indication) setup
- Wrong cipher suite ordering
- Missing OCSP stapling
How to Fix Your Server
Update TLS Configuration
Support TLS 1.2 minimum, but TLS 1.3 is better - it’s faster and more secure.
NGINX:
ssl_protocols TLSv1.2 TLSv1.3;
ssl_prefer_server_ciphers off;
Apache:
SSLProtocol all -SSLv3 -TLSv1 -TLSv1.1
SSLHonorCipherOrder off
Use Strong Ciphers
Use AEAD ciphers like AES-GCM or ChaCha20-Poly1305 for better security.
NGINX:
ssl_ciphers ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305;
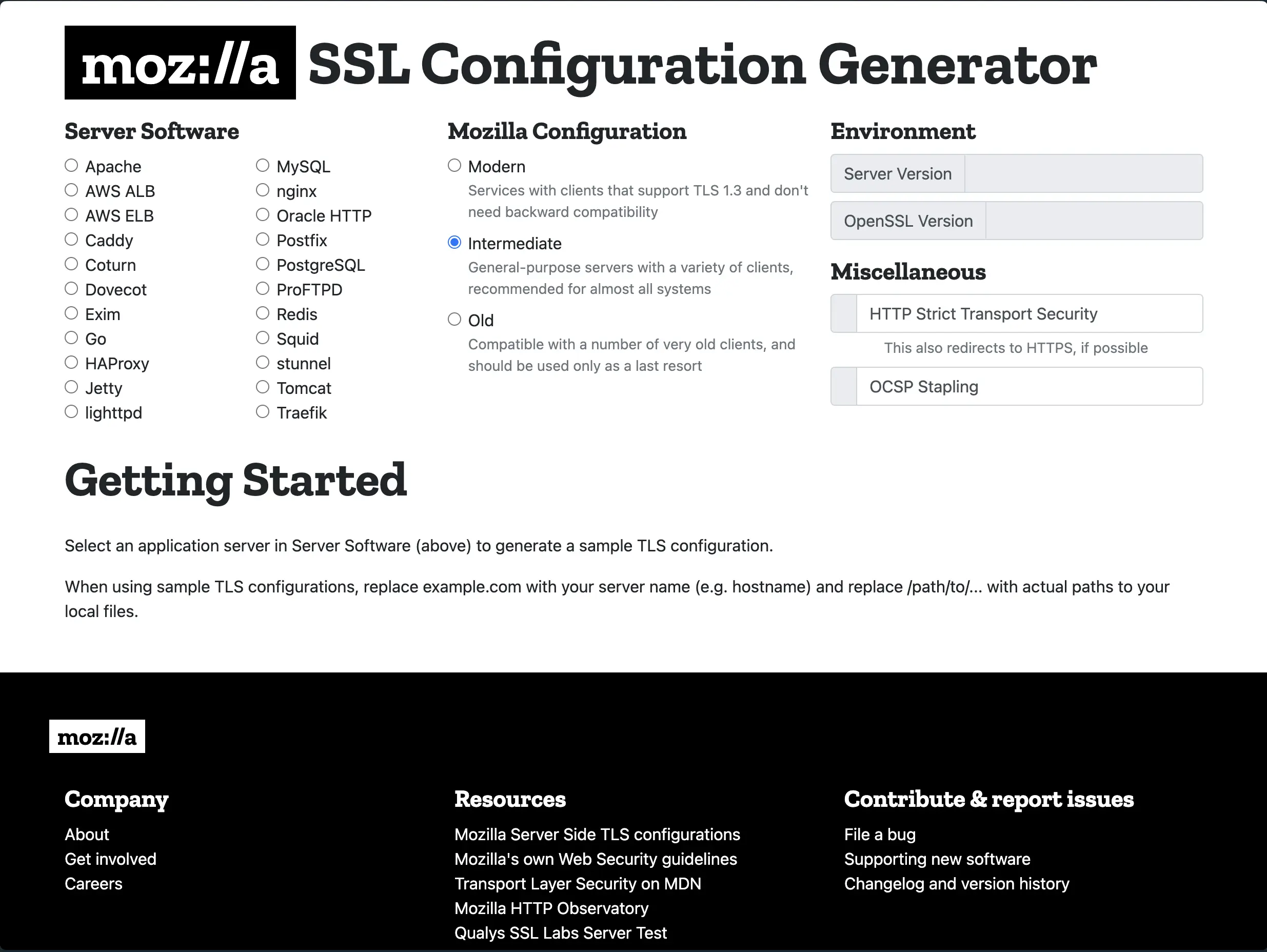
Use the
Mozilla SSL Configuration Generator for secure configs tailored to your server.
Fix Your SSL Certificates
Use trusted CAs like
Let's Encrypt (free),
DigiCert, or
Sectigo. Install the complete certificate chain including intermediate certificates.
Set up automated renewal with Certbot. Nothing’s worse than your site going down due to expired certificates.
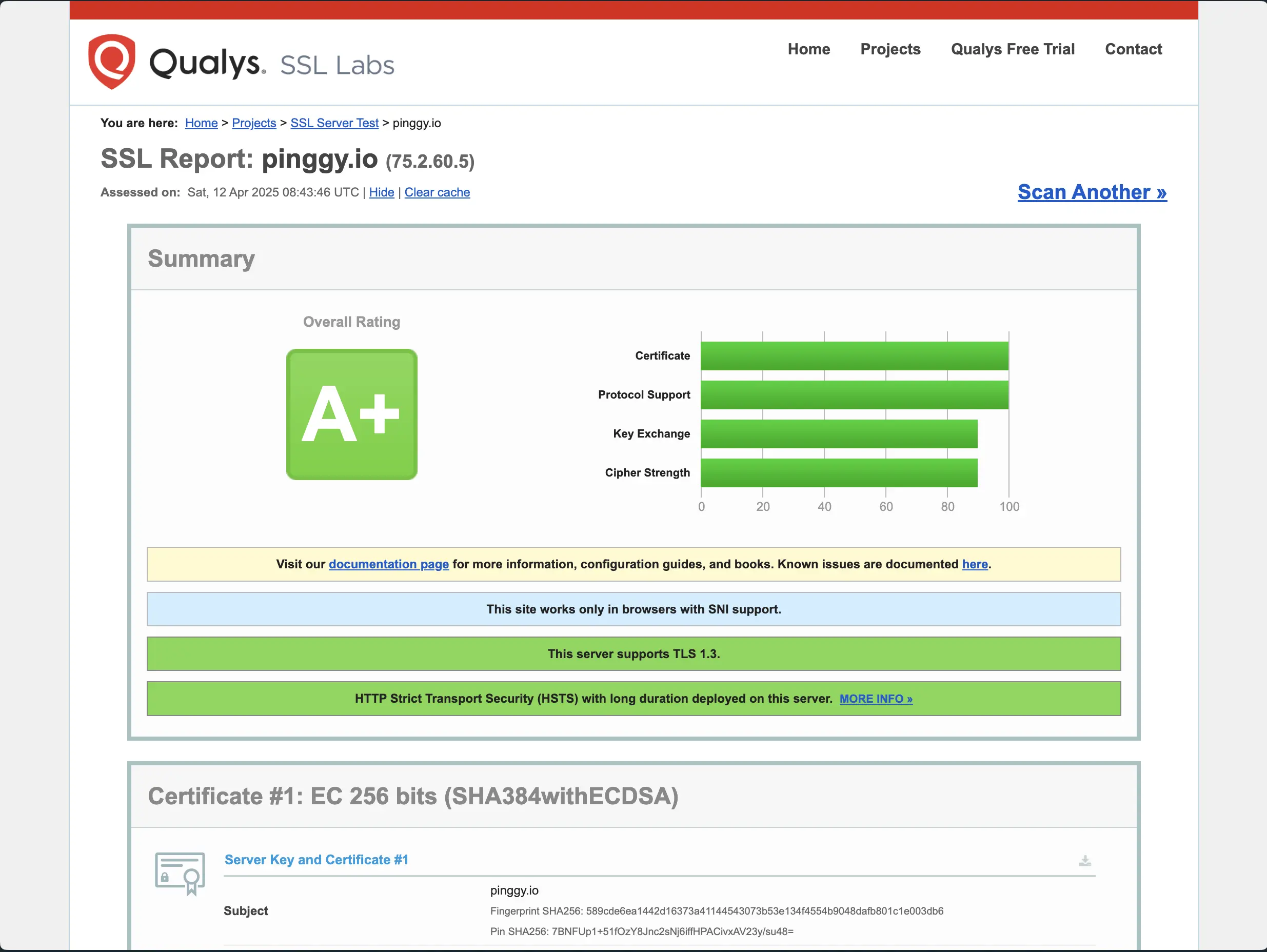
Test with SSL Labs
SSL Labs gives you a free security audit and grades your setup A+ to F. It checks protocols, ciphers, certificate validity, and vulnerabilities.
Keep Software Updated
Update Apache, Nginx, and OpenSSL regularly. These updates include TLS features, security patches, and performance improvements.
Enable HSTS
Force HTTPS connections and prevent downgrade attacks:
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains; preload" always;
Why This Error Kills Your Website
SSL errors are conversion killers. When users see “Your connection is not private,” 70-80% bounce immediately. That’s lost customers, leads, and revenue.
Traffic Loss - E-commerce sites are especially vulnerable since users won’t enter payment info on sites with SSL errors.
SEO Penalties - Google demotes sites with SSL issues. Chrome shows scary warnings for non-HTTPS sites.
Brand Damage - SSL errors scream “amateur.” Users associate them with sketchy sites and malware.
I’ve seen e-commerce sites lose thousands daily due to SSL issues. One misconfigured renewal can cost more than years of certificate fees.
Browser-Specific Fixes (Last Resort)
Chrome
- Disable QUIC: Go to
chrome://flags/, search “QUIC Protocol,” disable it, restart - Reset Settings:
Settings > Reset Settings > Restore defaults (wipes everything)
Firefox
- TLS Settings: Type
about:config, search security.tls.version.min, set to 3 for TLS 1.2
Safari
- Update macOS: Safari’s SSL is tied to OS security frameworks
- Clear Keychain: Open Keychain Access, remove bad certificates
Prevention (Never Deal With This Again)
Automated Monitoring - Use
SSL Labs API or services like Pingdom to check SSL health weekly.
Automate Renewals -
Certbot handles Let’s Encrypt renewals automatically:
# Runs twice daily with random delay
echo "0 0,12 * * * root python3 -c 'import random; import time; time.sleep(random.random() * 3600)' && certbot renew -q" | sudo tee -a /etc/crontab > /dev/null
Keep Updated - Enable automatic security updates for your OS and web server software.
Monitor User Reports - Set up feedback mechanisms but verify issues yourself.
Conclusion
ERR_SSL_VERSION_OR_CIPHER_MISMATCH might seem annoying, but it’s actually your browser protecting you from insecure connections.
For users: Update your browser, fix your system clock, clear cache. If multiple browsers fail, it’s the website’s problem.
For website owners: This is your wake-up call. Modernize your TLS setup, use strong ciphers, maintain certificates, and test regularly. SSL errors kill conversions and hurt SEO.
SSL errors aren’t just technical problems - they’re trust problems. Don’t give users reasons to doubt your site’s security.